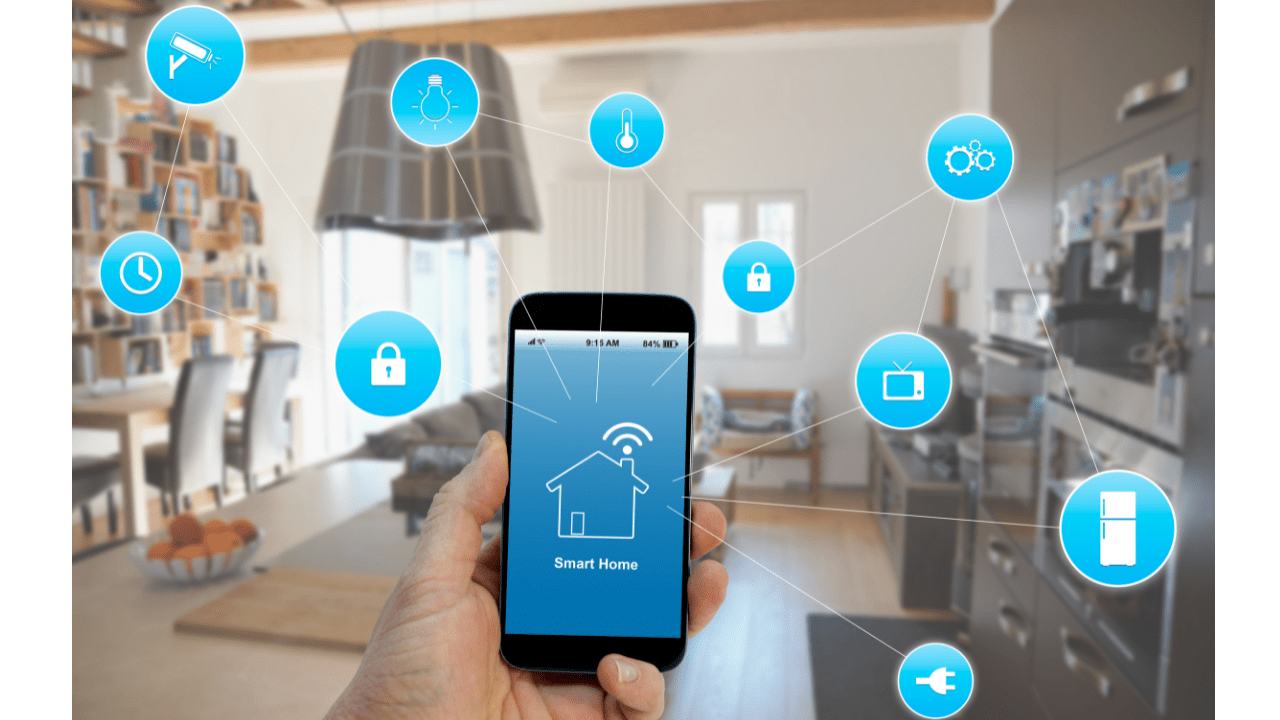
Home technology can be hacked. Anything from a coffee machine or LED light to a TV or a doorbell. We understand the risk of being vulnerable on our tablets and phones, but you’ll be shocked to realize how much data is collected from our other smart devices and how those very same devices can lead to a much wider compromise. Many of us don’t even know how many devices are on our connected networks, so we better listen up.
Today’s guest is Amanda Fennell. Amanda is the Chief Security Officer and Chief Information Officer at Relativity. In her role, she is responsible for championing and directing their tech and security strategies including risk management and compliance practices. She has a Master’s degree in Forensic Science and over 15 years of experience in Forensics and Cyber Security.
“The number one security problem is keeping things up to date.” - Amanda Fennell Share on XShow Notes:
- [1:12] – Amanda explains Relativity, her roles in the company, and how she was drawn to this field.
- [3:35] – Many people assume Amanda has all the new and greatest technology but knowing the risks of exploitation, she is selective.
- [4:25] – There are a multitude of devices that people don’t even realize they connect to their network.
- [5:23] – Because of the sheer volume of devices, hackers can do a sweep and use the information gathered.
- [6:32] – The number one security problem is keeping things up to date.
- [8:16] – Amanda walks through the simple steps of hacking smart devices.
- [9:40] – Amanda demonstrates how hacking something seemingly inconsequential can lead to accessing more.
- [11:23] – You need to know what’s connected to your network. You have more than you think.
- [12:41] – Surprisingly, there are connected lightbulbs that people sacrifice security for ease of access.
- [14:02] – When guests come over and you share your password, did you take their access back?
- [15:15] – Amanda is a big fan of segregating your network. She describes what this means.
- [16:29] – How can you segregate your network?
- [18:08] – Amanda suggests using WireShark.
- [19:39] – Many people hang on and use old routers because they still function, but most are not supported with updates after just a few years.
- [21:18] – It is also common practice to use identifying information as passwords and device names.
- [22:33] – Even Direct TV can be hacked. How can this be used against you?
- [23:30] – Amanda shares an investigation and how she used a printer spool file.
- [25:06] – Medical devices, printers, and copiers can be hacked.
- [27:29] – Amanda describes the differences between two security companies and what she advises doing to stay secure.
- [31:40] – How can you implement ongoing monitoring and detection in your home network?
- [33:52] – Implement updating devices into your monthly or weekly routine.
- [36:03] – You can do a scan on your network and even ask a friend for help.
- [37:28] – Smart coffee and smart fridges seem simple but can be used for targeting phishing and even when you are leaving the house.
- [39:33] – Just making yourself a little less accessible could deter a hacker because others will be easier.
- [41:43] – Amanda shares how false donations were used in fraud.
- [43:25] – We all deserve to have our information private and secure but it also needs to be personally accessible. That’s the risk.
Thanks for joining us on Easy Prey. Be sure to subscribe to our podcast on iTunes and leave a nice review.
Links and Resources:
- Podcast Web Page
- Facebook Page
- whatismyipaddress.com
- Easy Prey on Instagram
- Easy Prey on Twitter
- Easy Prey on LinkedIn
- Easy Prey on YouTube
- Easy Prey on Pinterest
- Relativity Website
- Security Sandbox Podcast
- Amanda Fennell on Twitter
- Relativity on Twitter
Transcript:
Amanda, thank you so much for coming on the Easy Prey Podcast today.
Thanks for having me. I'm excited.
I'm excited as well. Can you give me and the audience a little background of who you are, what you do, and why?
OK, the why is the easiest answer. Who I am is so existential. I'm Amanda, and I'm Chief Security Officer and Chief Information Officer at Relativity. We are a legal tech and compliance company based out of Chicago. Honestly, I feel like not many people have heard of us unless you do, like, eDiscovery and things like that. You've been around like EnCase or something.
The easiest way to say—it’s like a Splunk for legal documents. We organize a bunch of legal stuff. Now we've gotten into the compliance realm. We organize a bunch of stuff so you can figure out what to do with it.
Nice. Why did you get into this field?
I got into the field of security, I think, because just naturally, archaeologists. That's what we do. We're nosy, so it's the same thing. I started my master's and actually had gone right into trying to do paleo hominid biology. They were like, “There are no full-time jobs here for that, right?” I was like, “Oh, man. Well, where can I do forensics but have job security and pay my student loans back?”
At George Washington, they were like, “There's a digital forensics program.” I was like, “Game on. I am going through that.” The Matrix had just come out, and I was really fascinated by that. I was like, “I'd love to know how to deal with computers. That looks really cool.” That was it. It became the love affair of my life.
Awesome. Let's talk about smart home security, because I doubt that there's anybody listening to this podcast that doesn't have at least 45 smart devices in their house.
That's true, depending upon how many children are in there, too. That's really bad.
Exponentially increasing numbers.
Yes.
Let's talk through some of the risks of smart devices, and then let's talk about what the heck we can do to mitigate those risks. We can talk about ways to eliminate the risk, but I think you and I are going to have the same answers—throwing out, unplugging it. That's the only way to eliminate the risk. Let's talk about what kind of devices have what type of risk and then we'll go from there.
I think the first thing is—let me set the stage that I'm not perfect either. We're on this precipice that we just admitted and we got to it, where we got some of the HomePods for Siri in the house because I just love music. We just got to this point years and years after because everyone assumes that I would have all of the latest and greatest technology everywhere. While that could be true, the reality is you also have a huge avoidance of it because you also know it could be exploited.
We just got to this point where I also have started to delve really deep into this, which is why this was such an opportune time to talk about this because I've been having to do so much research on it. I guess the first thing is, let's talk about why this attack, what happened, and what they're doing. It's the easiest thing to target. The sheer scale and target, so surface attack reduction.
There are just so many different targets out there. Every house does have a multitude of IoT devices that people may not even realize that's what they're doing. You may or may not have a fridge that does this. Your Peloton, baby cameras, external storage devices, these things are just all across the place that everyone can get to them. If you've bought a TV in the most recent couple of years, I guarantee you, there's a way to hack through it.
If you've bought a TV in the most recent couple of years, I guarantee you, there's a way to hack through it. -Amanda Fennell Share on XI think the first problem people face is that the sheer multitude—they’re all over the place. They're in your house, whether you recognize it or not—your coffee machine, whatever. These things are there. I guess the part that's hard for people is that everyone walks around with that persona almost like, “Nobody would hack me. What does anybody want my information for? I don't have that much money in my bank account. You're welcome to it.” Those kinds of dialogues.
The reality is, you don't have a team of 50 hackers in a room in Russia saying I need to get into Amanda Fennell's coffee machine. They may be now after this podcast, but they aren't before. What they're doing is a commodity. It's just a large sweep. It's like that Spaceballs comb the desert like, “Just go for it.” That's what's happening. There are so many devices out there, they're getting attacked, people are grabbing information, and then they're doing what they do best.
They're reusing passwords. They're getting into different stuff. Then that's where the real money comes in. I guess that answers the question in a long way. There's a lot of places, a lot of stuff.
Also, the other effect of consumerism of, “We're always looking for the cheapest one.” That, to me, always resulted in the one that's going to be the least maintained, that's never going to have a firmware update. If there's some flaw, it's never going to get fixed.
Oh, man, you're hitting all of the great security problems. The first thing is the Costco dynamic. Everyone who goes to Costco is like, “Ah, great, they’ve got security cameras here. I'm just going to get this five pack of security cameras.” You're right, it's probably a bundle of some type or Smart Hub of some type, things like that.
By the way, Costco doesn't sell any of the Apple HomePods, which was a little disconcerting. They just have Google Home and Alexa. Also, Target, the same problem. What's going on there? People need to be a little bit more friendly to my Apple. But they get these devices, they go for the cheapest, and then you're right. The number one security problem is keeping things up-to-date.
The number one security problem is keeping things up-to-date. -Amanda Fennell Share on XEveryone's always like, “Oh, there's this huge breach.” The really big simple answer is, “Well, are you up to date? Are you patched? If you are, you don't have to worry.” But guess how many typical consumers are doing that? Very few—47% of devices that are in security cameras on home networks are vulnerable. That is painful. That's almost half.
47% of devices that are in security cameras on home networks are vulnerable. That is painful. That's almost half. -Amanda Fennell Share on XThere's an additional problem with that. I have security cameras. I did some research and, “OK, this is what I'm going to get.” I bought it through Amazon. I can admit that. I got it and played around. OK, it does great. I tried to be really good about my firmware updates. I got a firmware update for it and it bricked the camera.
But the microcontrollers. That's the problem. The microcontrollers are those 50¢, $5 chip that's installed, and it's just cheap. It is the problem.
It bricked and I contacted the manufacturer. They said, “Well, that camera, that's not a US version of the camera. That's the camera for Central and South America.” I'm like, “Oh, gray market stuff on Amazon.”
That's true.

So great security. Let's walk this through. You bought this camera, you tried to be a good steward of security to update this and everything. Great, great idea. The question is that when it connects to your network, whenever it is working, it connects to a network, and then you have the problem that so many people just have their default router passwords.
That takes me less than 60 seconds to google which one I want to hack through. It's really simple. This is so sad. I feel bad because I feel like they're going to listen to this and hear this. I was at a neighbor's, I was feeding the cat, and I decided to go in their hot tub. I was like, “Yeah, I'm going to go in your hot tub. It looks great.”
I said, “What's the Bluetooth pairing password to connect to the sound system or whatever?” Because I love music. They were like, “We just set up and we've never been able to figure that out.” Literally, 30 seconds later, I was like, “Oh, it's this and that.” They were like, “What?” I was like, “Uh-huh.” They were like, “How did you find this?” I was like, “I was only being polite by asking.”
Anyone who works in security can absolutely find this information by googling for 60 seconds. You connect these things to a network, then it's visible. Here's the fun part: everyone has this idea of like, “Oh, what's the big deal? It's my Bluetooth password or whatever.” These things lead to other things.
What does a bad person do to an adversary—bad guy, bad girl, et cetera, a bad day, I guess. We got pronouns now. If you've got this situation going on, they're trying to get something. A thermometer in a casino lobby aquarium was hacked. They accessed the network and extracted all of the casino's high roller database with the sensitive details from this. A thermometer in an aquarium, people. These things lead to other information.
When you have something connected to your network and you choose to not keep it up-to-date, which you did, you choose to connect it to a network that has default passwords and is not being patched, and you're not doing good security of prevent, detect, respond, monitoring, detection, and so on, it's just a downward spiral at that point.
Yeah, that's crazy. Also the same amount of issues with, I assume, routers and potentially modems. Let's dream that people are actually being appropriate and updating their IP cameras.
Updating this firmware is the thing, but yes, let's say that configuring the router. We did this big initiative when COVID happened. We realized that my risk profile changed. People weren't coming into the office anymore. Now, all of a sudden, I had to trust people in their home network—holy Hannah in a handbasket. That sucks.
I don't trust people on my home network. Then we did a huge education push for how to make yourself safe at home, for you and your family. Because a lot of people had kids that had Zooms, and the Zoom bombing thing took place and so on. So we really did a big push for education about this. But it was about configuring that home router, turning off the inbound network for everything except the services that run in the house.
Do you even know what's connected? It's the number one thing when you start is, “What am I supposed to be protecting?” You need to know what's connected. What's going on in your house? You mentioned people have somewhere between 40-60 devices at any given time. Well, two parts to that.
Number one, I doubt everyone on this podcast listening knows that. If they go and look in their router right now and look at the connections, they're going to be like, “Oh my God, why is Joe Kowalewski's phone hooked up to my network?” You have no idea how easy it is to get there. Really, changing the default passwords, turning off that inbound network traffic, and taking a look pretty often. Making sure you're not running web servers on 80 and 443; it shouldn't have any external traffic. These are some default things that you just have to update.
What do you think are some of the devices that people forget are internet-connected, or just in their mind, it's not really an internet-connected device but it is?
Oh, gosh, LED lights. That is one. The light bulb thing has been driving me crazy. I don't have these, by the way. They scare me. We were talking now even though we've said this here, but with great power comes great responsibility. First of all, who can't quote Spider-Man? You have to put this out there.
This dynamic of like, “Yes, I'm going to have light and I'm going to be able to turn it off because my kid forgets to turn his light off at night or something.” The capability of then allowing someone to figure out how to get into my network and do lateral movement just because I wanted the ease of access for a light bulb. That was one that really threw me off. Everyone, I think, is scared of their baby monitors. I think that one's made it out. I think people know.
We still keep hearing a baby monitor breaches left and right.
It's so scary. It's our most protected thing and we don't protect it well.
But I think that's at least why people are concerned about the baby monitor because they see that as like, that is the embodiment of vulnerability in that crib over there. So they can at least visualize what the risk is. But when you’re talking about your LED smart light, what's the risk of a smart light?
Yeah, I don't think people realize it, but that goes back to that same idea of once you get in, there are two main things you want to do. First, you elevate your privileges. The second one is you start to poke around. And third, you try to take something. You’ve got to elevate, lateral, and exfiltrate. These are the things that we want to accomplish when we're doing […]. I don't think people realize the connection of it.
I think one thing that is a weird one that people may not realize is when guests come over and you share that password in some capacity—even if you put it in the device for them or so on. Did you take their access back? Because when you didn't and they left, you've just given somebody the walking orders for how to get into your network. You’ve got to trust their security then.
Yes. I have a few wireless technology devices where I've had to give a vendor permission. I'm in the process of like, I'm calling them back to have them hardwire everything because it's like, “No, I don't know that your installer is not going to drive up next to my house.” Heaven forbid, I need to change my Wi-Fi name. I don't want to have to jump through the hoops of like, “How do I reset this 20-year-old piece of hardware that has a Wi-Fi connection?”
This is true, but this is one of those things that I would say is like the big hit home for people who have IoT and you're not sure what to do and so on. The first thing is to make sure you reset your defaults. Don't make it so easy for people. Number two, know what's connected. But then the next one is—and I'm a huge fan of this—segregating the home network because I absolutely have separate networks.
First of all, my kids, come on, that is a walking risk right there at all times. Minecraft and Roblox? I'm sorry. I don't know if I'm going to trust their security all the time. The great PlayStation hack from our era. These are the things you’ve got to concern yourself about. I sure hope my children know good security, but that doesn't mean I trust my 10-year-old and eight-year-old.
You’ve got to segregate your network into those different pieces and make sure that you do that. One of those would be guest access. I don't mean to make my house like I'm a corporate headquarters. But legit, I have a guest-separated network.
That, I admit I do, but because of COVID, no one's used it.
Yes, I know. It's been wonderful. Look, I live in New Orleans. People are starting to try to knock down the door. They don't care. There are Delta, like no, they don't care. How about just Mardi Gras coming in?
Exactly. Clarify for the audience what the heck a segregated network is.
- When you have any signal of network, the simplest way I would say this is you—so you have a couple of different operating abilities there if you want faster networking and so on. But if you take that, there are ways to put pieces of your network and say, “This is a separate VLAN; this is a different IP subset.” It can sound really complex to do all of those things. But I would guarantee you, if you actually google segregating home network, it's really simple to assign those different IP subnets.
Moving your DHCP block from your home router, which is currently 172. Whatever, it's really simple, and making that something that's not so obvious. This separation of your network and blocking that up into pieces. I would say also, doing this in a way that makes sense. I actually have one. Oh my gosh, here we go. This is a great reconnaissance right now for anybody.
By the time this changes, you will have replaced it with something different.
I will have replaced it all. Yes, and everything will be changed. One of them is for entertainment-type things. So TVs, any of the music devices, and so on, that is in one. It's an entertainment function. There is one that is all my business—just mine because my husband also does stuff at work and so his is separate. But I have one that's just my business, which is protecting my company. That's what I care a lot about.
Then I have one for guests, and then I have one that is for my kids because, man, is that full of just absolute trash. I've got these all four things separated very much the way I like to have my life—nice and orderly. But then I like to do a little Wireshark on that because this one—just download yourself Wireshark if you don't already play around with it and just look at the wired or wireless networks that you see are talking, what they're saying to whom, and stop things that you don't like.
A lot of routers are actually already defaulted that you can do all of that just by logging into your router and getting in there. If you don't know how to log into your router, I guarantee you I could tell you in about 60 seconds. Get in there. But yeah, you just separate your networks into these different areas and this IP space that you have.
Do most residential, low-end routers now support segregation?
I actually don't know if low-end residential routers do that. What a fascinating question, because I hate to say, I absolutely invested in something really expensive because I was really scared. I actually don't know, but I'm thinking about it.
I think most of them at least have a guest network and a non-guest network. I'm 99% confident of that. I haven't bought a D-Link router in 20 years, so I don't know.
It's a very good question, but I do know that the last time I had to play around and look at one for someone's house, I did see on their main login page there was a segmentation. I would say yes; I’m going to go out on a limb. It's been 20 years since you were doing it. Yes, I say we're right. We're going to say yes.
I'm sure there are people listening that have a router that is probably 20 years old.
Yes. Is that firmware updated? Is it patched? These are all great questions.
No, it's not updated. It's not been patched if it's 20 years old.
Would it even matter if it was at this point?
It's probably not even supported anymore. Most of these types of residential, very low-end products, they're probably supported for two or three years and then it's gone. The company doesn't even think about it anymore. They don't provide any support.
I think one of the things that are normally legacy that hangs out when people have the same thing set up for a long time that they don't realize how much they're giving away is the identified information. I think that, yes, people might have routers that they've had for a long time and maybe they need to patch them, update them, or change the default password. But I think I'd add on there.
It made me think of it because you said D-Link and we have someone on our team in IT whose name is Daniel Link. That's his picture and Zoom is a D-Link. It did make me think about it. The wireless SSID, people often will put in apartment numbers. I don't know who set up your internet, but somewhere along the way, they have all been taught to name it the most horrible thing, which is your address. Then you see people on the other end of the spectrum, which are just mean, and they say mean things.
I was in an airplane and I was traveling with, at the time, our CEO of a company. I remember I was having a hard time getting a signal somewhere. So I was like, I'm just going to take a look and see what's out there. Then I looked and I was like, “Hey, why is your phone named your name, like your full name?” He was like, “Huh?” And I was like, “Dude, if I wanted to hack you, this would be step one to find you.” I was like, “This is just horrible.”
But I would just say this identifying information is another one that people don't update the hardware, the firmware. They don't get their things patched. They also leave that right out there. Again, it's that theory of like, “Who cares about it? Who cares if I get hacked?”
You will because it's not just you, it's the other people in your family and your loved ones. It could be that they're actually trying to exploit your mom who just retired and she is a great person to steal the Social Security benefits from and so on. When that hack happens and you realize that you're the vector, it's painful, and you don't want to be that. I think that's one of the far-reaching ones.
I would also think you probably don't want to identify the manufacturer of your wireless router. A lot of times you see like, we're picking on D-Link today. It's D-Link 85312. OK, well, I now know I'm going to limit my attacks to just D-Link products.
OK, well, now I'm going to look around. I'm going to just press because I want to see. Here’s another one, by the way, that I see that comes up and people don't realize is an Internet of Things thing that they have to worry about—your DirecTV. If you have DirecTV, it is absolutely a signal that can be hacked.
If you have DirecTV, it is absolutely a signal that can be hacked. -Amanda Fennell Share on XAgain, I think people think like, what does it matter if they hack my DirecTV? Well, walk it out. It's my favorite thing to do: walk it out. They then know what you like to watch. They then know how to send you a targeted spear-phishing email that says, “”Amanda, I know you watch Game of Thrones every night and you're obsessed with it. So hey, So-and-so from Game of Thrones is actually going to be in town, and here are free tickets to have dinner with them.
Targeted spear phishing that can take place. It will be so targeted you would never think that this is some commodity thing or something. It's the little information that gets out there that people don't realize. Printers, yes. I love this. I love this network around here because I can see all these different people and what they're doing.
Yeah, people have printers. I could drive by the neighborhood and print something out on their printer.
Also the spool file. This has been dramatic lately anyway. But I will say in forensics, it was always my favorite thing to pull that file to see the last things that they had printed or the most common things printed and so on. Man, there was one investigation I was on one time when it was actually directions on where to bury a body. I'm not even kidding.
Oh my goodness.
That it was in the printer file that you were like, “You are kidding me that you literally printed this out in Google Maps,” kind of thing. It was actually back before Google Maps, but yes, you can find out a lot.
But that reminds me of like—I don't know if this was the case now but probably still is. There was a number of years ago and I don't want to date myself by how many years ago it was. There was this big investigation on companies that were buying used industrial printers, really, really like way over market value. People are like, “Why is this incredible used market for industrial photocopiers?” It's because they had hard drives in them.
They were buying photocopiers from police stations and lawyers' offices. The companies weren't thinking, “Oh, all these legal documents that we've photocopied are on a hard drive in the middle of the copy machine. We don't even know what collects data.” Almost the scarier thing is like, yeah, the concept of my phone is this walking, talking liability, but you don't think that your copier could be revealing stuff about you.
Then there's an entire area between if you make the jump into medical devices. This became huge in the last few years. The FDA had confirmed at St. Jude's that they had implantable cardiac devices that could be easily hacked, and that they were able to remotely access and control Medtronic insulin pumps. You think at the time, “OK, who cares? Number one, why would you hack that and who cares?”
First of all, it's not always a commodity. There could be other reasons for it. There could be something that's just very targeted for whatever reason. Maybe people don't like vets and they're going after people in the Veterans Affairs, and those hospitals and so on. Activating someone's insulin or a cardiac device, done. You're done.
The jump is that, number one, people don't know the power of the devices that they have and what information they're gathering. Number two, they walk around feeling like, “Oh, it doesn't matter. It wouldn't happen to me, and it doesn't matter if it does.”
People don't know the power of the devices that they have and what information they're gathering. -Amanda Fennell Share on XYeah, that's crazy. I know even DSLR cameras now can be internet-connected. They can jump on your Wi-Fi so you can send your photos. Before we started recording we were talking about alarm systems. My wife and I were walking around the neighborhood and noticed that this was more of a phishing thing, but everyone who has an alarm system has a sign on the front door that says, “Hey, we're using ADT.”
Great, now I know what alarm company you're using. Now, if I'm spear phishing trying to get into your house, I know who you are already because that's why I'm at your house. Now I know you use ADT. You’re now revealing even more information about yourself.
I think everyone's going to have like—you put people in these shoe boxes in life of like, “OK, crazy security person, et cetera.” OK, I have two alarm systems, so let's just get this out there now. OK, I have two. It's because I don't trust just one. I like to compare data between the two and so on. I like redundancy. I like user entity behavior analytics to try to figure out what is that kid's window doing open at 2:00 AM?
The first thing I'd say, from my experience from both of them, is that one of them has definitely learned the power of what they have. Yes, a lot of people are going to have that targeted information to try to get in. They've definitely rolled out all of those two factors, multi-factor authentications, and validation verification before they'll let you log into something. That part's great. I would say that that part's awesome.
The other company to remain nameless has not rolled it out strongly. It's opted in. I would say that that's one thing to look for when you have these. First of all, yes, I agree. If you're going to have a sign in the front, don't use it from the actual company you use. You should definitely have, I think, it's the red herring. It's like the thing that throws people off.
Exchange signs with your neighbors.
Yes. It's a great idea. It's an absolutely fantastic idea to do that. Then the second one is making sure you've got some kind of verification—two-factor authentication that's validating you whenever you log in to anything. The other one, which I find very concerning, is that you can often, and the rings are very prolific, and a lot of people use them and stuff for many devices. A lot of that information does get uploaded to the cloud.
That's also the question of like, “How is that secure?” You have to make sure that there's security there. There's a lot of trust that goes on whenever you trust somebody's cloud. I think that's one of those things I would put out there. So yes, I think it's a great observation. We hope that people walk away from this listening and change their signs.
When you're talking about the doorbells, I forget who Amazon's brand is. Was that Ring? Did Amazon make the Ring? I don't know.
They convert so Alexa can work with it, yes.
I think Amazon bought Ring. Amazon rolled out this, “We're going to create this product called Sidewalk where we are going to basically allow other devices to get on your network through our doorbells.”
See, this is how it starts.
The marketing was like, “That way if other people's doorbells—their internet connections go down, they can keep the doorbells up and running.
It's not a crowdsource, man.
But it's exactly what they're doing. They were crowdsourcing internet connectivity. I don't believe it was necessarily an opt-in. I think it was actually an opt-out. They automatically rolled out this feature that you had to turn off, otherwise, other Amazon devices could use your Wi-Fi with their own little ad hoc security. You're going to decide that you're going to let other people on my network do stuff without my permission because of a firmware update?
I think this goes back to one of those fundamental points of number one: Know what's going on, identification. Know what's going on. Number two, monitoring the ongoing connections. That can be done easily by looking at your router and saying, “What the hell is going on over here?” But I think that's where you don't always know what you have signed up for.
In this day and age, it's like, what was in a South Park episode? The Apple agreement that people were signing and you were signing your life away? Because the Apple agreement at this point for iTunes was like 72 pages. No one knows what we're signing anymore and what you're agreeing to. We just skip to the end checkmark because we want to get to whatever it is that we want. I would say that to counteract that, ongoing monitoring and detection needs to be done in your home network.
Ongoing monitoring and detection needs to be done in your home network. -Amanda Fennell Share on XHow do you do ongoing monitoring and detection? I know there are apps that you can get for your phone or another wireless device that will scan your network looking for devices. Based on the MAC address, it'll tell you, “Hey, it's an Apple device, it's a TiVo, or it's an Alexa device.” Sometimes it's an HSBC widget and you have no idea what it is.
I feel like in every cliche, you're saying, “I do have a device that does that.” You're right, I do. With all things, if we talk about IT and security, it's always people, process, and tech. The people in the house that care about security, unfortunately, I'm the main harbinger. So I'm the people. I'm the one that implements the process. I'm the one who determines who's getting on and who's getting off. It's very much like Gladiator. I'll decide if you're going to get on there.
Not today.
Not today. I would say that I actually do deploy a device that does scan all of that. It also sends me an alert anytime somebody joins my network and it does tell me, based on the MAC address, what kind of a device it is. Some of those are a little bit wonky, I've got to tell you. I had bought a couple of laptops for some Minecraft love for my kids. I was configuring them to be kid-friendly, A.K.A. couldn't do anything bad from my standpoint.
It came up that it was some random Chinese manufacturer's device, and it didn't say that it was. I was like, “What in the hell?” End result: yes, people, process, and tech. I implement it, I am the people, and I am the process. The tech is what helps me the most, and it is something that has automated that and lets me know who's joining. Then I can also kill the connections and I can also take the time and say nothing after 11:00 PM or in this case, 9:00 PM, et cetera. I do think you should lift and shift that responsibility to some tech if you can. There are a lot of things you can do.
That's something that's run without disclosing the brand of the router because we don't want to do that here. Is that something that has run at the router level or between the router and those devices?
It does. I would almost say, if I could give it the description in a way that's imaginative, let's just consider it like an umbrella that wraps around my router. It is the go-between, it is the middleman that is hanging out in that area. When something wants to connect, it's got to talk to it. It's like the bouncer at the club.
Got you. I'm going to take a step back because we talked about the process. We talked about people, we talked about process. How often should people be checking for firmware updates on their IoT devices?
Obviously, the answer is every day. That's not going to happen. I would say that if you think about it, if you implement it into some kind of thing that you do naturally. Let's say that you do your bills every month and you go and you open up your spreadsheet, and you make sure you pay your bills maybe every Friday or something. If you would implement it into a pattern that you have already to be scanned for updates, then it would be helpful.
There are some devices out there that will automatically scan for updates and let you know an update is pending. Do you want to do this now and reset and so on? That's great. If you have that option to do automatic updates, I would opt in for that. Unfortunately, with some phones, it can be a draw on the battery. But I would say otherwise, opt in if you can.
At the minimum, I would say you've got to do this monthly. At the minimum, monthly. Quarterly is at least you're doing something. Weekly would be great. The updates don't really come out as often as you would think, but there is patching and so on that does need to happen. I'd say that's a great way: just implement it into one of the normal routines that you already know that you do.
I like that. That makes sense. I think that's accessible. It's not like I need to check every single automated light switch every day for an update. You spent half my day updating.
Also just scanning your network like getting a scanner. A free open source you can get scanning and you can scan your network for any vulnerabilities. This is what we do every day at work. Why wouldn't we use this for our home environment and say—and you can have fun with this. I do this with my 10-year-old. I'm like, “All right, let's see if we can hack mommy's network today. Let's take a look at this.” So just get a free open source, download a scanner, scan your environment, and see if any high vulnerabilities pop out at you. You'll be able to see if you've got something.
Are there any particular open source scanners that you'd recommend?
There's none that popped to mind that I'm like, “This is the number one thing that I would scan with.” I've used probably 10 different ones in my life and they're all great. Now we have so many for work that everything is not open source. Open source always helps, but making sure you know what's out there, those kinds of things are super helpful.
Worst-case scenario, if you are feeling overwhelmed by the concept of doing something like a scan, you should find someone you do trust and ask them to help you and work with you. Because everyone knows that person who likes computers, and I would say get that person and say, “Hey, I'll get you a bottle of wine, come on over on a Friday night. Let's take a look and see if I've got any vulnerabilities.” I’ve got to tell you, I've made a lot of friends that way and not because they'll invite me over. “You seem good with computers.” “All right, cost you a glass of wine.”
As long as it's not just, “Just come on over. Oh, hey, while you're here, would you mind looking at….”
That's my mother-in-law. That's totally true. “By the way, while you're here….” I'm like, “OK, here we go.”
Let's see, have we missed anything here in this discussion about smart home IoT? To me, I think the stuff that I'm afraid of is the stuff that I don't know exists or the stuff that I didn't ever connect. You talked about the smart coffee maker or the smart fridge. Those are things that I just don't see the benefit of enabling, personally. I think those are the things that if I had one of those devices in my house—I know I don’t—but the risk of those devices if they're broadcasting their own connectivity, if they're broadcasting.
Two parts. First of all, people don't see the risk associated with it because it seems simple. I have a coffee machine, I set it up, and it basically knows my schedule that I'm going to have coffee at 6:00 AM and I have a second cup at whatever other time. So OK, now we can do targeted spear phishing towards Amanda. She's a coffee junkie. Not a surprise. But the second thing also lets people know potentially when I'm leaving the house, when your house is empty.
It really goes back to this concept of reconnaissance. I know you know all about kill chain. This is like, who doesn't love kill chain? Let's go back to 2008, let's get into it, but reconnaissance is in step one of trying to attack something. In Sun Tzu’s, Art of War, you need to know your enemy kind of thing. Any information is helpful.
That coffee machine seems so minuscule, but it does tell you whenever people aren't there, potentially. Whenever they're leaving, that refrigerator tells people when you're not there and whenever your house is empty and vulnerable.
When you're on vacation, make sure that lights are still turning on and off on the same schedule that they turn on and off when you're actually home.
Oh, crazy. I'm in it. You should do a different schedule. Absolutely, yeah.
Realistically, there should be randomness when your lights turn on and off, whether you're there or not.
Yes. I think there's also a deterrence factor that can be bypassed as well, I think, by just a little bit of a wall. It's really always in security then about from the very beginning, I had something I want to protect. I'm going to put a castle around it and I'm going to protect these “crown jewels,” which by the way, crown jewels are not really greatly protected nowadays. They're totally accessible.
OK, so we put a castle around something I want to protect, and then I'm going to protect it more. I've got more money. I'm going to put some people in charge to protect it. Then I'm going to build a moat, a bridge, and all these other things. But the one thing that you really have to do is just build it enough that you're not attractive.
All you have to do is not be the slowest person in the herd. Just build enough of a wall that you're not easily accessible. It can be done by just updating that firmware, patching, changing the default passwords, such simple moves that you made yourself just a little bit less accessible. The neighbor next door, I guarantee you, hasn't done those things. They're going to be the one that gets hacked.
Then my big one: your router admin password should not be your Wi-Fi password. I think most people just think, “Oh, I just want to remember one password for my network.” The password that they give out to their friends when they come over to use the house because the Wi-Fi is the same password that that unscrupulous person goes in and, on a bad day, logs in.
Yes. One, they're using the default password. Two, they're using the same password that they use. This is a great point. Three, they're just reusing a password that they use often and they don't understand the importance of it. That is also the password for their bank account, which again, maybe you don't have any concern about it, but they are able to overdraft you, or they are able to use your information to create a fake ID and do Social Security claims against you and so on.
These are things that a password would be used for, which always drives me nuts. But yeah, what a great point. I don't know why people do that, but I have come across it.
They use your bank account as an intermediary fraud.
How so?
The scammers, they've taken over your account and you don't know. They send money into your account and then they funnel it off to somebody else. The police come calling. They come to you and say, “Why are you laundering money?” And you're like, “Huh?”
Actually, I saw something that was a case that I was on about a year ago. Not related to my company. Just putting that out there. I did see something where it was a nonprofit. They found their bank account had all these transactions added in, and they were super confused. It turned out that it was the card company—like a PayPal kind of situation—had been hacked. So they'd gotten a bunch of different people's information, and they were testing it. They felt like the one fastest way to test it would be as a donation to a company that was an NGO because nobody cares or tracks that.
You're accepting donations. You're not going to question.
Nobody is going to make you do a captcha on that website when you make a donation; they just want the money. They went to a company and they did that. It was super sad because this company woke up one morning with $30,000 added to their account—really excited. They were like, “Oh my God. We finally have been found out and people care.” No, you have to give all that money back, actually. None of those people donated it, but they were just testing it. The intermediary was painful there.
Yeah. That's why you want to always keep tabs on your bank accounts.
That's right. Keep an eye for any activity. Also, a lot of those banks nowadays, they've got the alerts set up. I love this one credit card that I have. They text me for anything. “Is this you?” “Is this a duplicate?” “Did you mean to tip this much?” I love that question because it makes me feel like such a good person. Like, “I did mean to tip that much, yes.” But I really do appreciate companies that go above and beyond with that kind of stuff to notice that the behavior is different.
I think that's where, in some sense, security and privacy is moving is finding that stuff that's abnormal.
Secure by default, privacy by default. We all deserve to have our information private and in a secure fashion, but it does still have to be available. That's the line we walk every day.
Yup. I guess it's like with smart home devices. We’ve got to figure out, is the benefit worth the risk? What can we do to mitigate the risk? The only way to get rid of the risk is don't install it, don't plug it in, don't bring it into the house. For some people, that's a good option.
Yeah. Like I said, I'm navigating it myself because I can't help it. I like to cook and I like to have my music on when I'm cooking. I’ve finally given into and capitulated. It is one of those things that you just have to implement those basic fundamentals of prevent tech response. You have to have a mitigation in place. You have to know what is normal, what is abnormal, and make sure you're monitoring that.
Perfect. I know you guys have an interesting podcast about security. Can you tell us about that?
I do. Speaking of cooking, this is actually one of the reasons why this came about. We often do what security teams do. We get together and during this remote time, we do a lot of happy hours remotely kind of thing. I noticed these conversations would just go on for like four hours, and they're hilarious. I got into an argument last week with a whole bunch of people about the way electricity works in Canada. This was a thing.
We get into these debates and everything, and I find them so fun that we finally decided to do a podcast where we pulled all of it together. Where people who are passionate about something unrelated to security and outside of work, we bring it into security. We have an external person who's an authority on something like archaeology, neurosurgery. We actually just did basketball two weeks ago and astrology the week before.
Some crazy concepts, but we get them on a podcast with somebody who's also an expert inside with security, HR, or something. We put the two together. We mix it up just like a sandbox and say, “OK, well, what do we create with this?” It is shocking how many of these things actually have great overlays, but it is the Security Sandbox. It's a podcast that we release every month, a new episode, and it's pretty exciting.
That's awesome. If people want to find you online, where can they find you and your company?
Yeah, relativity.com, not Einstein, which I think everyone thinks that's what Relativity is, but no. So relativity.com. If you go on there, you just search for Amanda Fennell, security podcast, or any of that stuff. You'll find it. We are on anywhere that you get your podcasts.
Awesome. Amanda, thank you so much for coming on the Easy Prey Podcast today.
It was easy to be here. Thank you for having me.
That's so kind.