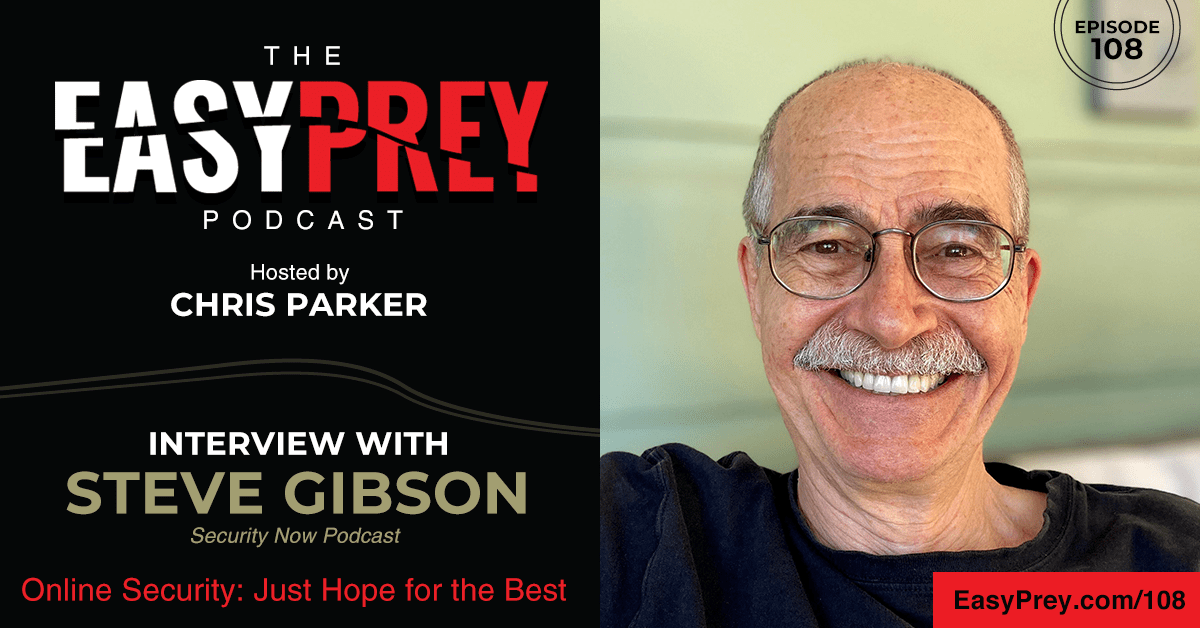
When the internet began, trust was implied. But today, how can you know who or what to trust on the web? Today’s guest is Steve Gibson. Steve has participated in the PC industry since its inception. He authored InfoWorld’s top rated Tech Talk column for eight years and he produces the TWiT Network’s weekly Security Now podcast in its 17th year. He developed a working replacement for the username and password site known as QRL and is best known for his 35 year old SpinRite mass storage and data recovery and maintenance utility which he continues to develop.
“Most consumers at this point just simply hope for the best.” - Steve Gibson Share on XShow Notes:
- [1:14] – Steve shares his background starting in the 70s.
- [2:41] – A personal experience inspired Steve to create SpinRite.
- [5:03] – When the internet was created, Microsoft wasn’t on board. They rushed the solution when they realized it was necessary.
- [6:06] – Because there was no firewall, people could see anyone’s C drive.
- [7:49] – In the beginning of internet use, there was implicit trust.
- [10:01] – Internet security has very complicated problems.
- [12:37] – We’ve created a complicated and constantly changing system.
- [14:03] – Steve’s podcast is geared towards those who implement security solutions for consumers.
- [15:40] – In many ways, the internet is “consumer hostile.”
- [18:43] – The system is so fundamentally prone to abuse that end users hope for the best.
- [21:10] – Steve and Chris continue to print authentication and recovery codes.
- [23:35] – The reason we’ve gotten into this mess is because in the beginning, the internet wasn’t very useful.
- [24:43] – The most commonly used password is still 123456.
- [26:39] – Password requirements make things even more complicated because everything constantly changes and every site is different.
- [29:01] – Steve shares what he thinks can help the industry, starting with certifications.
- [31:21] – Things are improving in some areas, including the federal government stepping in to regulate some things.
- [33:18] – Steve discusses regulation pros and cons.
- [35:12] – The internet has revolutionized efficiency and potential.
- [38:54] – There should be courses on how to search the internet for things.
- [40:26] – It is important to continue improving this powerful tool.
Thanks for joining us on Easy Prey. Be sure to subscribe to our podcast on iTunes and leave a nice review.
Links and Resources:
- Podcast Web Page
- Facebook Page
- whatismyipaddress.com
- Easy Prey on Instagram
- Easy Prey on Twitter
- Easy Prey on LinkedIn
- Easy Prey on YouTube
- Easy Prey on Pinterest
- Home of Gibson Research Corporation Website
- Steve Gibson on Twitter
- Security Now Podcast
Transcript:
Steve, thank you for coming on the Easy Prey Podcast today.
I'm glad to be here, Chris. Thanks so much.
You're very welcome. Can you tell me and the audience a little bit about your background, who you are, and how many of us have used your products?
I'm probably older than all of the rest of everybody.
Both of our products are probably older than most people listening to this podcast.

I thought that was dumb, so I wrote a little piece of code to fix that problem. When I was looking for a second something to do for the PC—actually, it was an ex-girlfriend's hard drive that had crashed and I sort of missed her. She said, “Steve, all my company's data, all of our financials for three years are on this drive; we have to get it back.” Of course, she'd never done a backup and so that was actually the birth of SpinRite, which was real-world data recovery. At one point, I thought, “I'll bet this would be generally useful.” That created SpinRite.
The real short story there is that it was the sector interleaving, which was SpinRite's real claim to fame. The idea is that you could re-interleave, change the low-level formatting on a hard drive to reorder the sectors to increase their performance. You could do that by leaving all the data there if you did it one track at a time. The problem is, if you're going to reformat a track, that's your last chance to get the data off of it. I had to build really robust data recovery into SpinRite before I dared change the formatting of a track.
Now here we are downstream 35 years; I'm working on SpinRite 6.1. All of the other stuff has gone away. Hard drives have been interleaved one-to-one. You can't make them any faster now for decades, but it's that data recovery side, which I invested so much in then and it's been evolving over time too. That's the thing that has held together and kept SpinRite relevant.
At one point in the past, when I had finished a major release, I was sort of done for a while, looking around for something to do, and we had local area networking, but we didn't really have the internet yet. We sort of had email, which we were using something called cc:Mail. I guess it ran around on DOS back then. Anyway, we had Novell and we had 10BASE2 with that thick coax that ran around, not even a twisted pair.
I thought, “OK, it's time to put the company on the internet.” We got an ISDN line and hooked it up. I don't remember exactly the chain of sequence, but of course, the internet surprised Microsoft. They were all going to go do MSN because we had the source, CompuServe, and AOL. In other words, all this dial-up stuff was what we call pre-internet, all of our modems.
When the internet happened, Microsoft looked around and thought, “Oh crap, we don't have an answer for this.” They got a TCP/IP stack from somewhere and just slapped it into Windows and are like, “Oh, now we have the internet.” Yes, but you also had file and printer sharing, and everybody had their drives connected to everybody else's.
What happened when the internet got added to Windows is that everyone's C: drive was not firewalled. It was on the public internet. First, it occurred to me, “Wait a minute, is this really happening?” Then I did a scan of the IP region around the IP that we've been assigned through the ISDN line and I was literally looking at strangers’ C: drives, which sounds insane to say it today, but this was 35 years ago. It was really what was happening.
Microsoft just rushed into this, get Windows on the internet, and security—calling it an afterthought is sort of an understatement. That's where Shields Up came from. It occurred to me that I could create a website that people could go to and, just as I had innocently mapped someone's C: drive to my computer in horror, this thing could check their computer for its ports to see whether they were exposing their files and printers.
Of course, that was 105.5 million tests ago. Since I knew I was going to be talking today, I checked the count yesterday and that's a good number because I do a list of IPs and don't double count even when people use it. It's sort of become a bit of a staple, sort of very much as WhatIsMyIP has become a staple on the internet. You and I have been at this for a while.
That got my foot into the security side and I've been doing both ever since. Hard drive data recovery, keeping SpinRite current. Although, I've been a little negligent on that front so I'm catching up. Then internet security has been a real interest because it's obviously a big problem.
I was wondering, because I was thinking about this, when the internet started there was almost this implicit trust—we think spam was not a thing. If my mail server handed an email to your mail server, your mail server trusted that it really was coming from me and not some forged email address. I think the same sort of thing with Microsoft allowing your C: drive to be shared was probably a mistake. It was definitely a mistake.
The way I would put it is it was a miracle that you could send an email to someone. “What? This works?” -Steve Gibson Share on XYou're right. The way I would put it is it was a miracle that you could send an email to someone. “What? This works?” It was incredible. As we know, the internet was never designed with any security. It was DARPA and then ARPANET. The idea that universities could actually send an email or create a group and correspond was a miracle. You knew all 10 people who were on the internet back then so it wasn't like they were strangers who had any access at all.
One of the things that evolved from my thinking about this as much as I have is just how not designed for real people this was. The fact that our mothers have to type http://, what is wrong with this picture? This was not designed for people. This was designed for techies and we've just foisted on to the general public who are like, “Boy, these people are weird who invented this thing.”
That has been constantly like, “Gosh, that's not really secure.” “How do we solve that problem?” “How do we solve that security problem?” “How do we solve that security problem?” “Oh, that fix caused a new security problem.”
Right. It's classic security as an afterthought. It's like building a house and not considering that you should have door locks. It's like, “Oh, wait a minute.”
It's classic security as an afterthought. It's like building a house and not considering that you should have door locks. -Steve Gibson Share on XWere there even doors initially? Initially, there were no doors. It's funny because I think back just even with the change from HTTP to HTTPS, that was like, “Oh well, that means it's secure. That means it's safe. That means you can trust that website.” Now, it's like, “Well, it no longer means you can trust the website, just that your data is encrypted between here and there.”
From one standpoint, it is the case that this stuff is complicated. Back 30 years ago, we were solving easy problems of security. The other big problem, of course, is cryptocurrency has created a way for bad guys to get paid without getting caught. As soon as you create a way for the bad guys to get paid without getting caught, then you give them an incentive to do bad things that are going to force people to pay them. We've created this new system.
Ten years ago, there were viruses, but they were there because you could do them. Kids were screwing around to see how bad an infection could be, but they didn't really do anything. Now, we have malware, we have ransomware, and it's really become a problem. When you create a profit motive for bad guys, then they're able to leverage the fact that there are still weaknesses in security. Your point is things are way better today, but not perfect.
Yeah, definitely not perfect. I probably don't go a day without hearing a story of someone losing money, losing access to data, and what can I do? A lot of times after the fact it's too late.
There's a comprehension gap, too, between the users of this technology and the creators. Those of us who are talking to each other like this, listening to each other's podcasts, and thinking about this, this is an entirely different mindset from the user who is just, “Wait, you mean I move this little puck on the desk and this pointer moves on the screen? How does that happen? Wait, do I right-click or left-click? When do I double click?”
Most users are barely hanging on to get their work done because what we've created is this bizarre system and one of your points is that it's also constantly changing. We don't leave anything alone.
Yeah, and I think that's one of those things that just frustrates people. They wake up the next morning, their computer has done an OS update. “How do I get to my word processor now? How do I get to Word? How do I get my email? Where did the button go?” It throws people for a loop.

I know you do your Security Now podcast and you talk about all the latest threats going on. Sometimes you're deep-diving into things that most people, probably might impact them, but they probably have no clue about was it the Log4j? For most consumers, it may impact them, but in their life, there's nothing that they can do about it and nothing that they even understand about it.
Right, and of course, the Security Now podcast is aimed at the techie audience crowd, not at the consumer level. It's sort of the first order of how these problems happened and then the Equifax problem where 140-some million users actually were impacted by having their credit exported from Equifax.
Yes, that becomes a different story to the users. Aside from Shields Up, do you do much discussion on consumer security threats?
I really don't. I guess the focus is largely on the technology being used to protect people. The Security Now audience is the people who are implementing that technology primarily. But like you, I have a family, I have friends, and they're like, “Tell me about phishing, and does that really start with a ph?” Yeah, I know.

Look what we've done. We've created a system where email is coming in and we've told them you cannot click on links. They're like, “But the email has links, and it's from mom.” We say, “Well, is it really your mother or is it someone in Russia?” It's so consumer-hostile. We have a system where we've struck terror in the hearts of users saying, “Here's a computer, but don't touch it.”
“Don't click on links in the email, don't go to websites, and by all means, don't use the computer on the internet because it's going to get corrupted.”
Right, or when you think you're at PayPal, you might not really be at PayPal. “Look up in the URL, very carefully look at what's written, and make sure it's an a with no umlaut.” What have we done? This is just so hostile to the consumer.
I really think that most consumers are like, “Well, I'm just going to hope for the best.” -Steve Gibson Share on XI really think that most consumers are like, “Well, I'm just going to hope for the best.” If you want an umbrella broad title for this whole mess that we've created, “hope for the best” is probably the best banner for this. If they do keep all these rules in their head: “I can't click on links, I have to carefully scrutinize the URL to make sure that it looks exactly right.” How are they even sure what exactly right means?
There's so much knowledge that an end user has to carry around with them as a consequence of the design of this system, which is really the classic case of evolution over the last 40 years. “I'm nervous about clicking on email links.” How does the typical end user survive this? I don't know. They hope for the best.
Yeah, I mean, that's true. I got a notice, I got an email yesterday, “Hey, your package has shipped,” and it claimed to be from UPS. I'm like, “I don't remember ordering anything,” so I'm like, “Is this a legitimate email from UPS? I guess I can wait until this thing shows up on my doorstep and hope the porch pirates don't get it before I do, or do I click on the link? Is it really from UPS, or is it a scam to try to get me?”
As a consequence of all this problem, for the year-end, I changed some of my banking stuff around, and interacting with my bank is incredibly painful now. They send me some email that they say it's authentic and I click on a link, which takes me to a website, where I log in to something to get another link to give me access to the document, which they need me to then bring up in a PDF viewer. I print it, then I have to sign it, scan it, and edit it.
The system is so fundamentally prone to abuse that end users hope for the best. Those who really have to have it work securely require incredible hoops to be jumped through. I have second-factor authentication on many of my accounts because I understand the need for it. My wife, I've not tried to get her to cross that rubicon.
She hopes for the best and I just make sure that if anything were to go wrong, she's safe. I'm imaging her computer in the background so she doesn’t have to worry about it. If it melts down, “OK, honey, we'll just restore from the image and we're good to go.” Sadly, it's a mess. On the other hand, I guess it’s a full-employment guarantee for all those who are in IT security.
I agree that the security measures almost become worse than the problem. I remember Troy Hunt and I were talking about security and authentication. What is the best security that you think the other person can tolerate and manage? Google Authenticator app is going to be better than SMS. “Google Authenticator, what is that? How do I set it up?” SMS, at least, is better. It's not the best, but it's better.
In the case of Authenticator, one of the things that I've noticed, because I'm a heavy one-time password user authenticator, is if you then need to set up another device, it's like, “Wait a minute, because that was all kind of half-baked.” I've been really conscientious about printing the QR code that I get to set up an authenticator, and so I've got a sheet of paper. In this day and age, the fallback is to print the QR code so that you could show it to another device when you want to clone your authenticator secrets. It's not ready for the world.
I've been really conscientious about printing the QR code that I get to set up an authenticator, so I've got a sheet of paper. -Steve Gibson Share on XThere are a few—and I'm going to be intentionally vague about this—product services that I use where they generate a recovery code. I have printed those recovery codes on a piece of paper and they're in a bank deposit in a bank, in a safe in a bank. Because there are things where the vendor basically said, “If you lose your authenticator, you lose access to your email, and you don't have this recovery code, we're not giving you access to this service.”
Which brings up another big problem we've created for the typical user, which is what happens when granddad dies and takes all of his accounts and all of his knowledge about how to do things with him? How do you gain access after someone is no longer competent to do that for themselves? As a consequence of the fact that the bad guys have become so clever, what that means is that we've had to raise the bar of proving identity in the event of someone becoming incompetent, deceased, or something. Now it's like, “Oh, a proof of incompetence or proof of power of attorney,” and it's like, “Oh my Lord.”
And then also turns into another problem. I had another service where somebody was able to very, very temporarily gain access to this platform by providing a fake passport in my name. They've provided all the documentation that the company wanted for, “You've lost access to your email, you've lost your password. Here, provide us these documents.” So they just provided forged versions of those documents.
Right.
Because they don't know what I really look like. “Here is my legitimate document—put this on file. If it ever happens again and it doesn't match this document, then don't release the account.”
I know. I think that's one of the ways we got into this trouble, too, is that in the beginning, it didn't really matter that much. There wasn't really any value on the internet, it was just sort of a big phone line, a big party line. People talked and my mom called it AWOL. She had friends and acquaintances. It was just sort of a big place where you did social things, but then business moved into the internet and onto the internet.
Banks were there and it then became not just all about fun and communications but the way the world was working. It started off with there was no value to impersonating somebody and it didn't really matter that much if someone did. It was like, “Oh, well, they guessed that my password was 123456.”
That's the other thing, too. That is still the most popular password, 123456. If that's the most popular password, that says something about the degree to which people still don't really care about their use. It's like, “If it works, fine. And if it doesn't, well, I'll just go and have lunch.”
It's funny because every solution to that problem creates another problem. It's like, “OK, your password is not secure, and we're afraid that someone's going to get your password, so you need to change your password every 90 days.” “Wait, what? So now it's 1234567?”
Right, or you put in a password. It's like, “Oh, no, sorry, it cannot be longer than 20 characters.” Some places, you cannot have a special character. In some places, you have to have a special character. Look what we've done. It's the most consumer-hostile system you could imagine.
Some platforms are like, “You can't use a password that even has so many digits similar to a previous password.” I'm like, “Wait, so you're storing unencrypted versions of my password to verify that my new password doesn't have pieces of my old password in it?”
That's a good point. The only way they could do that is if they did not have a hash of it—they had the actual thing.
How was that safe? How in the world is that like…? “Fine, I'm just going to use simpler and simpler passwords.” So there goes security.
You're exactly right. Again, the user is just hoping for the best. They don't understand this. This all seems really weird and bizarre. Why does this website login I have to do this, and over on this website I have to do that? There's no consistency between them.
As you said, even individual sites are changing from time to time, apparently, on a whim. It's like, “Oh, we decided to do it this way.” There are sites where I've not logged in for a long time whose password requirements have changed since I last logged in, so my old password is no longer accepted because it doesn't make it through the browser filter saying, “Oh, no, no, that's not valid.” It's like, “Wait, it was last year.” It's like, “Oh, no, no, so it's OK.” Now, password-recovery time. “Well, we're going to send you an email.” “Wait a minute, I don't have that email account anymore.” I mean, it's just all broken.
Yeah, and that's what I get from people also. “Hey, I have to reset my password, and I don't have access to the email that I used when I originally created the account, what do I do?” “I don't know. If it's your bank, go there in person. But if it's a Google service, who are you going to call? They don't have a phone number.”
Any rational person stepping back from this would have to conclude that this is still the Wild West. It feels all lots of technology, all this stuff is happening, and there's commerce, communications, social networks, and social media. Thank goodness for all of the technology we had when this COVID outbreak occurred because a lot of us were still able to continue to work, do business, have meetings, and all that. You have to think that eventually—I don't know when, not apparently during our lifetime—but someday this will be different. Someday this will be fixed, but in the meantime, it's a lot of fun.
Do you see things on the horizon that give you hope that there are things coming that will unify, simplify?
One of the problems is medicine is slow-moving and stodgy but very careful. It’s, at first, do no wrong. Don't harm the patient, and you have to be certified in order to be a medical practitioner. We do certainly have certifications in our industry, but they're not requirements.
Anybody can create some software, and we've just seen this with, for example, this little Log4j nightmare that we were talking about that is basically a vulnerability that affects so much of the internet. Some well-meaning people created software, but they weren't professionals. They were advanced hobbyists and they did the best job they could. Unfortunately, in retrospect, there were some things that should have been done differently.
I guess my point is that even today, we're in a system where we're using software written by people we don't know with no requirement that they have any particular proven certified skillset, and it seems to work and it's popular, which of course, means nothing because popularity isn't a guarantee of correctness of software. Everyone starts to use it. Years later, we discovered that it's got a big problem.
Similarly, no two sites have the same password requirements because there's no universal requirement about that. It is really an everyone-for-themselves system. There are signs of things getting better. The US federal government is beginning to get much stronger about insisting that federal agencies act in certain ways with a certain speed. Certainly, the C-Suite executives, with these last couple of years of ransomware, they're understanding now when their CIOs and their security people say, “We need more money,” because of course, it all ultimately comes down to budget, time, and brand personnel.
They're not being blown off as quickly as they probably once were because security is something now in the front of the minds of executives running companies. They recognize that they're at real risk. The Federal Trade Commission just said that in the same way that they sued Equifax for negligently not patching a long-known problem for years, which ultimately caused that huge consumer action and loss of data, the US Federal Trade Commission just last week said, “If companies are irresponsible in not patching for this Log4j vulnerability, they stand to be sued if, as a consequence of that, consumers are harmed.
This is new. That's not something we've seen before. Much as I hate the idea of arbitrary regulations raising the cost of doing business—because one of the ways we've kept this so economical is that it's not been a heavily regulated industry—well, if we can't do it ourselves, if we can't self-regulate, then it may be necessary for the government to come in and do that.
Of course, over in the EU, we see that their consumer protection agencies have become extremely heavy-handed. On one hand, it's like, oh, boy, this is going to the whole GDPR and what it means. On one hand, yes, it's more expensive. On the other hand, maybe that's what it's going to take.
I think the challenge behind that is while we can say the US government can impose restrictions and mandates on US companies, all of a sudden, my favorite website, is it hosted, developed, and managed by people in the US? Is my favorite app hosted, managed, and developed by someone in the US or they're somewhere else in the world where their government has not chosen to enforce these requirements?
Right.
Not that I'm advocating for a one-world government or anything like that, but because the internet has made anyone who has an internet connection anywhere in the world can now participate with the global audience, it does push the issue much further than just our local economies.
Right. When I hear you talk about globalization and the fact that anybody anywhere can do this, I think the flip side of this is just think of the value that that creates. We've spent some time being all gloom and doom about security, but the fact is, this has created a revolution in efficiency, economy, and enabling a level of potential that we've never had before.
You and I can think of anything we want to know and put that into Google. Within a minute, we have information at our fingertips, which is phenomenal. Yes, we haven't figured out how to do it perfectly yet, but boy, for those who know how to use this tool is it awesomely powerful.
Think about the person who has a unique skillset in a country where that skillset is not marketable. It has a customer base from every other country but theirs to find customers to use their skillset. They don't have to have a company with them that specializes in that skillset to market for them. That individual can go out and find a world of potential customers. To me, that's one of those awesome things about the internet is it's such a game-changer for so many people in places where they don't have access to some of the resources that we in the US have access to.
Sometimes, college-aged kids will ask me, “OK, what should I do in life?” It's a question that I get enough that I've thought about it and that my answer has been to find something that you truly love and become the best at it. That means, absolutely, the 100,000 hours, how many thousands of hours it takes, but be the best.
What the internet does, exactly as you're saying, is once upon a time some town may have had, just to use an example, the most amazing world-class plumber that anyone has ever seen. This guy could just plumb anything, so this town had amazing plumbing because of the level of skill that he brought to this. The problem was adjacent towns didn't have access to him, didn't even know that he existed because there was not perfect communication. The internet creates perfect communication.
The idea is that in days past, you could have somebody who is incredibly skilled at something, but that skill would go unrecognized due to lack of access to it. Exactly to your point, what the internet creates is that kind of knowledge, that so-called perfect communication where other people are saying, “Hey, we've got a really bad plumbing problem over here, we don't know what to do. The other five plumbers that we've tried to get to fix it haven't been able to do it.” It's like, “Oh, I know who you need,” and sure enough, that town's best plumber has an away mission in order to go fix something else that he wouldn't have otherwise been able to do.
Or he now has a YouTube channel where he teaches his excellent plumbing skills.

Boy, isn't that a phenomenon too? I had a finicky door lock on my car and my buddy, who's a YouTuber said, “Oh, just go look up on YouTube how to fix that.” Again, anything you want to know.
Maybe this is for people closer to our age and this doesn't apply to younger people—there should be courses on how to search the internet for things.
Yeah.
People will call me to say, “Hey, Chris, how do you do this?” “I have no clue but hold on a second, I know what to search for to find it. Here, go to this website. This will tell you how to do it.” Maybe I shouldn't use Google, but knowing how to google is a skill.
In fact, one of my favorites is that there was a period in my life where I was going to Starbucks every morning and we had sort of the Starbucks group that had amalgamated. We all became friends and we knew about each other's lives. From time to time, I have something with me for some reason and then they'll say, “Where'd you get that?” I just look at them like, “Amazon. What are you talking about? Where does everything come from?”
That is so incredibly true. It's not all doom and gloom when it comes to the internet. There's a lot of positive going on out there.
I think that's absolutely true. Certainly, we need to secure it, we need to keep working in that direction, and we need to make it better. Conversations like this where we do a little spitballing and think about, “OK, well, what are the things that haven't been addressed yet? What is the potential future?”
We need to have these because it's people like us who are going to be coming up with next-generation solutions. Even if it's just making it a little bit better, we need that. But at the same time, oh my God, what an amazing facility has been created here for the world.
Yeah, it really is. You and I are both employed by it in a sense. It is a great thing.
Let's wrap up here. If people want to find you on social and online on this great, wonderful World Wide Web, where can they find you?
The home of my work—since I'm Steve Gibson—is Gibson Research Corporation, grc.com. I am on Twitter. It's @SGgrc. That's pretty much it.
Awesome. Thank you so much for coming on the podcast today.
It's been my pleasure, Chris. Absolutely, thanks.